Data protection and information security compliance teams regularly need to account for the changes in the privacy regulatory landscape. The firm hold of GDPR in modern commerce is ever-present, with enforcement of the regulation proving that no matter where an organization is based or where a cybersecurity breach may have occurred, the European Union’s regulatory reach is global in nature.
The most recent fine was announced at the end of October, when the ICO fined Marriott International Inc £18.4 million in relation to a data breach that occurred within a company it acquired. What it signals even more deeply than ever before is the need to perform highly detailed due diligence from a cybersecurity perspective prior to entering into any M&A deal.
GDPR’s reach is global, but what about the other headline grabbing laws, such as the California Consumer Privacy Act (CCPA)? Based on an analysis of the differences, companies with a global reach would be better off implementing strategies that allow for flexibility that guarantees compliance in all jurisdictions. However, “better off” in this context just means avoiding regulatory scrutiny and enforcement. The CCPA contains a substantially different way of handling opt-out rights for the sale of personal information which the GDPR lacks. There are also differences in handling information of those under 16 years of age. The differences go beyond the aforementioned details, and it is important for the data protection officer or other responsible compliance officer to run a compliance program recognizing and handling all of the relevant risks not just for GDPR and CCPA where applicable, but also for regulations around the world that may touch a business’ activities.
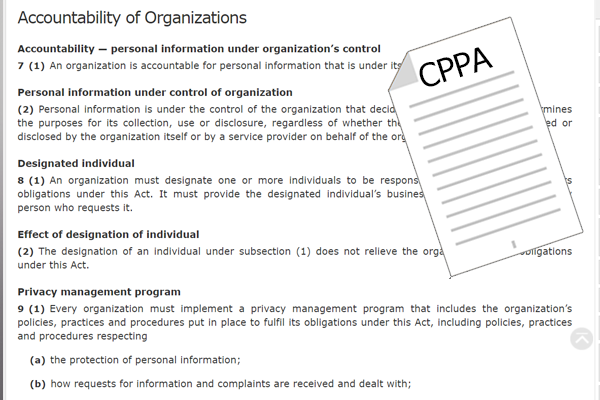
Of particular note is Canada’s upcoming privacy legislation dubbed the Consumer Privacy Protection Act (CPPA). If the acronyms do not create a headache for the compliance officers, they will for the market generally as they struggle to get fluent with all of the regulatory jargon. With increments of regulation beyond GDPR and CCPA, the CPPA (see, the juxtaposition of the acronyms is already nauseating!) requires the maintenance of a “privacy management program” which is similar to the GDPR’s accountability principle‘s requirement to put in place appropriate technical and organizational measures. The differences are present, however, and the relevant officer needs to take into account explicit requirements mentioned in the CPPA, and should the organization also need to demonstrate GDPR compliance, then the relevant evidence of technical and organizational measures should be provided as well in the organization’s overall privacy program.
Generally, the responsible officer needs to (1) know about their organization, where they are located, where data comes from and goes to, who is using that data and when, (2) understand regulations around the world that may impact the way in which that organization can work with the data mentioned in #1, and (3) set up and enforce a compliance program that ensures the organization as a whole has a mechanism for being transparently compliant with those regulations.
With the plethora of privacy regulations to consider, the hope is it will be easier for businesses to have uniform comprehension of what they need to do, but often the legislative bodies deliberating future regulations do not have the luxury of taking into account the combination of local, regional, and global contexts. It is important to recognize that businesses and consumers in the digital world all have to spend additional time taking into account the increasingly wider set of regulations they may or may not be bound by, and there is the legitimate concern that a growing industrial complex around these regulations will prove only to hamper economic progress rather than foster it. This is not to suggest that the aims sought within individual privacy legislation is not important, rather I stress the need for simpler comprehension on the local, regional, and global levels.